This three-day training session is organized and delivered by Oxford University faculty. It will discuss in detail the challenges and opportunities of the modern information society. These are not solely or even primarily technical in nature – they also involve elemental questions of political culture and institutions, public policy, ethics, law, and diplomacy.
Where: Tallinn University of Technology, Ehitajate tee 5, Tallinn, room U01-202 (auditorium behind the main hall)
DAY 1: September 4, Friday, Grand Hall
09:00 – 10.00 Registration and welcoming
10:00 – 10:30 Course Introduction (Lucas Kello)
10:30 – 12:00 Lecture 1: Computing and Networks: The Basics (Andrew Martin)
12:00 – 13:00 Lunch break
13:00 – 14:20 Lecture 2: Code as a Weapon: Worms and Viruses (Andrew Martin)
14:20 – 14:30 Short break
14:30 – 16:00 Lecture 3: International Security and Conflict in the Cyber Age (Lucas Kello)
16.00 – 16.10 Short break
16:10 – 17:00 Day 1 summaryDAY 2: September 5, Saturday, Grand Hall
08:30 – 09:00 Registration
09:00 – 10:20 Lecture 4: Rules of War in the Cyber Domain (Lucas Kello)
10:20 – 10:30 Short break
10:30 – 12:00 Lecture 5: Cybersecurity and the Age of Privateering: A Historical Analogy (Florian Egloff)
12:00 – 13:00 Lunch break
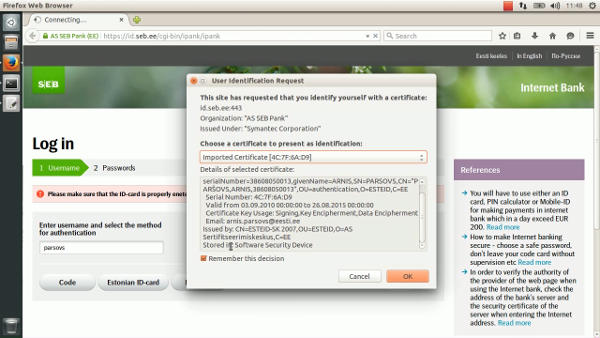
13:00 – 14:20 Lecture 6: Origins, Principles and Functions of the Estonian State Information System (Kuldar Taveter)
14:20 – 14:30 Short break
14:30 – 16:00 Lecture 7: Designing User Friendly and Secure Services of e-State (Kuldar Taveter)
16:00 – 16:20 Coffee break
16:20 – 17:00 Day 2 summary and simulation exercise briefingDAY 3: September 6, Sunday, Grand Hall
08:30 – 09:00 Registration
09:00 – 09:30 Simulation exercise set up
09:30 – 13:00 Simulation Exercise
13:00 – 14:30 Lunch break and group discussion
14:30 – 15:30 Post-Exercise Debriefing: Decisionmaking in a Crisis
15:30 – 15:50 Coffee break
15:50 – 17:00 Course summary
Registration open until 02.09.2015.
Links:
http://www.egov.ee/oxford/