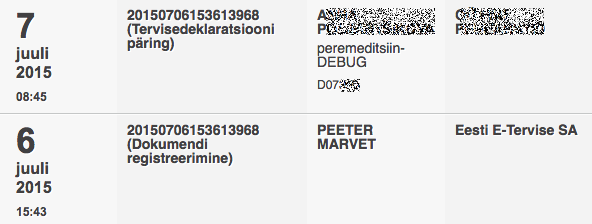
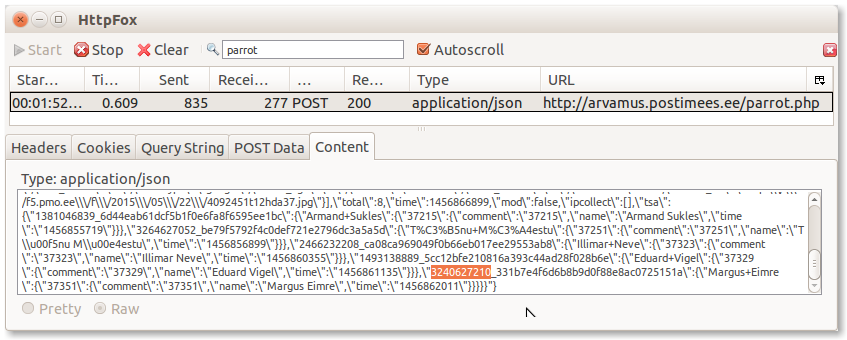
From the March of this year everyone is able to check on the eesti.ee portal, which state agencies have reviewed their data from the population register. The new service is a matter of grave concern to notaries who are required to make inquiries into the population register, for example, if it is necessary to find out whether real estate may be the joint property of spouses or former spouses, or if it is necessary to organize succession proceedings based on data, including identifying potential heirs. According to Eve Strangi, Chief Executive Officer of the Chamber of Notaries, after the Data Tracker service came into being, people who did not use the notarial service themselves, but whose parents, children or spouse had done this, also came to the notice that personal data was viewed.
In most cases, people can get information that their data has been viewed, but not always. “An exception, for example, is the situation where heir data is required to make a will. However, the will until the death of the maker is secret, and the existence and content of the act can not be disclosed to the heir earlier than specified by the law.
Heiko Vainsalu, Head of the State Information System Agency X-Road, said that the Data Tracker highlighted weaknesses in information systems, which should now be addressed by the authorities themselves. “It is now up to the authorities to eliminate them – to improve the logic of data services and to find data services better suited to specific needs. Besides the ability to track the use and processing of the data in the state information system, the Data Tracker helps to highlight and correct the design mistakes of information systems.”
Some filters are needed. For example, the queries made by law enforcement institutions in investigating the crimes must not show up to the subjects in the Data Tracker service.
Links:
http://arileht.delfi.ee/news/uudised/andmejalgija-paljastas-notarite-salajased-toimingud?id=78131976