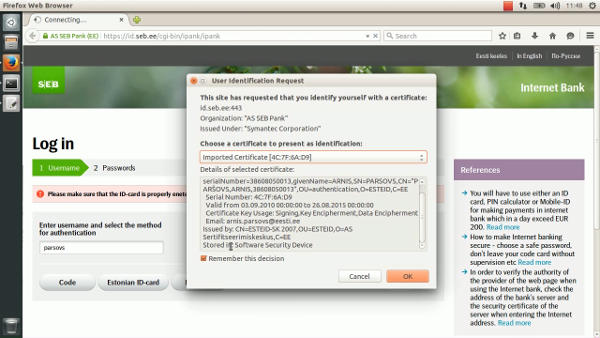
The flaw in SEB Estonia Internet bank allows to login just by knowing the victim’s username. The consequences of the flaw go beyond the read-only access to victim’s transaction history. The victim can be impersonated in any website that supports authentication through SEB (eesti.ee, mnt.ee, tele2.ee, etc.). The flaw can be abused to buy goods from online merchants (as shown in the video) since SEB does not require signature authorization for “banklink” transactions.
Timeline:
2015.05.11. 13:00 – reported to CERT-EE
2015.05.14. 12:00 – fixed by SEB Estonia
The time that was required for SEB to fix such a critical flaw surprises a bit.
SEB’s response:
SEB spokesman commented that “referred security issue existed in so-called laboratory conditions meaning that it needed several conditions to coincide and a specific knowledge”.
“Security issue got fixed and we also checked that the flaw was not maliciously exploited” said SEB’s spokesman and added that the problem got fixed faster than in an hour, after all the needed information was received.
Anto Veldre (RIA): It is better that ethical people with academic degree are looking for security holes than cyber criminals doing it. People should understand that new technology is complicated, systems at home and servers need to have updates everyday there is no such a thing like secure system (security) but there are people and control methods, if there is a problem it will be handled and afterwards logs are checked if something really happened.
Silver Vohu (SEB): It took less than an hour to make a fix. But reproducing the situation took most of the days and asking additional questions from CERT-EE was needed. In normal situation it was impossible to reproduce the problem.
Links:
https://www.youtube.com/watch?v=rRB8jZnS5nY
http://forte.delfi.ee/news/tarkvara/tosine-turvaauk-seb-internetipanka-sai-sisse-ainuuksi-kasutajanimega?id=72291205
http://tehnika.postimees.ee/3306453/seb-internetipangas-oli-tosine-turvaauk-sisenemiseks-piisas-vaid-kasutajanimest
http://seitsmesed.ee/eesti/uudis/2015/08/26/tosine-turvaauk-seb-internetipanka-sai-sisse-vaid-kasutajanimega/
http://www.tv3play.ee/sisu/seitsmesed-uudised-2015/648229

