An Empirical Comparison of Approaches for Security Requirements Elicitation
Abstract: Security Quality Requirements Engineering (SQUARE) and Security Requirements Elicitation from Business Processes (SREBP). This thesis compares the two methods based on an empirical case study of the Estonian Football Association. The elicited security requirements are categorized and the completeness of their coverage is compared.
Student: Karl Kolk
Curriculum: Cyber Security (MSc)
Supervisor: Raimundas Matulevicius
Reviewer: Fredrik Payman Milani
Defense: 26.02.2015The Analysis and Design of a Privacy-Preserving Survey System
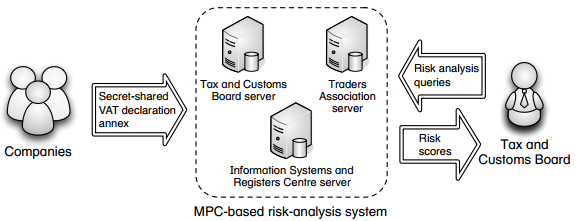
Abstract: This master’s thesis describes the design and business processes of the prototype of a secure survey system using secure multi-party computation. The design of the system is also described in this paper and is illustrated with a deployment model.
Student: Meril Vaht
Curriculum: Cyber Security (MSc)
Supervisor: Dan Bogdanov
Reviewer: Raimundas Matulevicius
Defense: 04.06.2015, 09:00, Liivi 2-405Pattern Based Security Requirement Derivation with Security Risk-aware Secure Tropos
Abstract: In this master thesis we investigate the integration of a pattern based security requirement elicitation process in the goal-oriented IS development. By performing this integration we aim at providing a process that enables the elicitation of security requirements from Security Risk-aware Secure Tropos (RAST) models. The contribution of this thesis are five Security Risk-aware Patterns expressed using RAST.
Student: Atilio Rrenja
Curriculum: Software Engineering (MSc)
Supervisor: Raimundas Matulevicius
Reviewer: Peep Küngas
Defense: 04.06.2015, 09:00, Liivi 2-405.Comparing Security Risk-oriented Modelling Languages to Manage Social Engineering Risks
Abstract: The paper applies structured approach in identification of one security risk management standard that can be applied with different modelling languages. For a more in-depth analysis in this paper considered several modelling languages as BPMN, Secure Tropos and Misuse case.
Student: Sarbar Tursunova
Curriculum: Cyber Security (MSc)
Supervisor: Raimundas Matulevicius
Defense: 04.06.2015, 09:00, Liivi 2-405.
Reviewer: Olga AltuhhovaAnalysis and Mitigation of Recent Attacks on Mobile Communication Backend
Abstract: This thesis presents a broad and thorough overview and analysis of the known attacks against mobile network signaling protocols and the possible mitigation strategies. The attacks are presented in a uniform way, in relation to the mobile network protocol standards and signaling scenarios. Moreover, this thesis also presents a new attack that enables a malicious party with access to the signaling network to remove lost or stolen phones from the blacklist that is intended to prevent their use.
Student: Siddharth Prakash Rao
Curriculum: NordSecMob (MSc)
Supervisor: Tuomas Aura
Supervisor: Dominique Unruh
Supervisor: Silke Holtmanns
Supervisor: Ian Oliver
Reviewer: Arnis Paršovs
Defense: 09.06.2015, 09:00, Liivi 2-405.Entropy Based Robust Watermarking Algorithm
Abstract: In this work, multiple robust watermarking algorithms are introduced. They embed watermark image into singular values of host image’s blocks with low entropy values. The quantitative and qualitative experimental results are indicating that the proposed algorithms are imperceptible and robust against many signal processing attacks.
Student: Lauri Laur
Curriculum: Software Engineering (MSc)
Supervisor: Gholamreza Anbarjafari
Supervisor: Mary Agoyi
Reviewer: Kaveh Khoshkhah
Defense: 09.06.2015, 09:00, Liivi 2-405.NFC Security Solution for Web Applications
Abstract: This thesis compares existing and possible security solutions for web applications, analyses NFC compatibility for security solutions and proposes a new NFC authentication and signing solution using Google Cloud Messaging service and NFC Java Card. This new proposed solution enables authentication and signing via NFC enabled mobile phone and NFC Java Card without any additional readers or efforts to be made.
Student: Jonas Kiiver
Curriculum: Software Engineering (MSc)
Supervisor: Eero Vainikko
Reviewer: Meelis Roos
Defense: 09.06.2015, 09:00, Liivi 2-404.Applying Estonian Internet Voting Individual Verification System to Other Electoral Systems
The current paper gives an overview of the Estonian internet voting individual verification system and introduces different ballot styles. It proposes and describes modifications to the Estonian system, so it could be used for individual verification with the introduced ballot styles and multiple elections.
Student: Joonas Lõmps
Curriculum: Informatics (BSc)
Supervisor: Sven Heiberg
Reviewer: Arnis Paršovs
Defense: 12.06.2015, 09:00, Liivi 2-404Secure Bitcoin Wallet
This report outlines various methods and solutions targeting security concerns and aims to understand their effectiveness. It also describes Secure Bitcoin Wallet, standard Bitcoin transactions client, enhanced with various security features and services.
Student: Sevil Guler
Curriculum: NordSecMob (MSc)
Supervisor: Sead Muftic, Vitaly Skachek
Reviewer: Arnis Paršovs
Defense: 27.08.2015
Links:
http://comserv.cs.ut.ee/forms/ati_report/index.php?language=en
http://www.cs.ut.ee/en/msc/theses/deadlines