The Estonian Foreign Intelligence Service (Välisluureamet) was previously known as the Estonian Information Board (Teabeamet).
This world is very fast and very good experts are required. Your homepage, which has become a little more informative recently, suggests that you are also looking for new people?
Of course we are looking. Do not we compete on the same market as other public authorities and the private sector? If we are talking about a big data or a better use of public sources in obtaining our information, then everyone with this competence is very much in demand.At the end of the annual report (Estonian version), I found one challenge. These who can solve this could work for you?
Since we have a publication once a year, where we talk about our work openly, we also intended to use this publication to expand our recruiting field. If people reach to the last page of the document, then there may be some who can solve the puzzle and send the solution to us. I can not guarantee that the solution ensures a job, as other processes need to be followed. However, it definitely shows that the person has competence and analytical mind in cryptography.You are giving interviews that would have been a big surprise many years ago. You reject the public myths about intelligence work. Your agency publishes puzzles to find potential employees. What is the future of your agency?
Yes, over the last few years, we have come out of the shadows and closer to the public. My clear view is that if you are not in the picture then you do not exist. However, if we want to recruit the best specialists, it is very difficult to find people for an institution that does not exist. Of course, we must at the same time be aware of security, but these risks can be handled. But in the future of intelligence, there are two keywords: co-operation and technology.
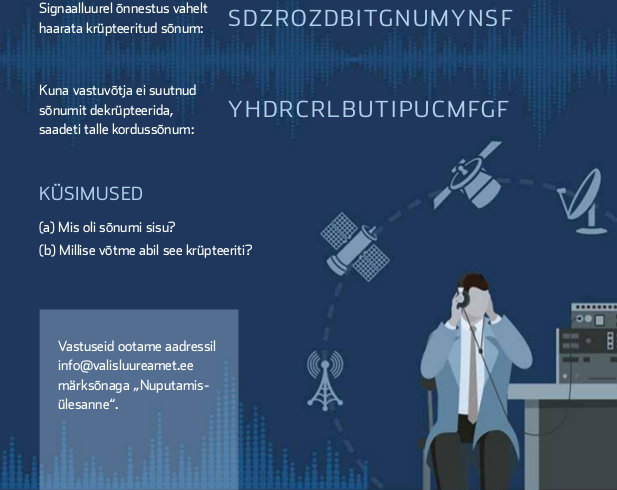
Crypto challenge:
Signal intelligence was able to capture an encrypted message: SDZROZDBITGNUMYNSF
However, the receiver was unable to decrypt the message and the message was transmitted again: YHDRCRLBUTIPUCMFGFQuestions:
(a) What was content of the message
(b) What key was used to encryptThe solutions can be sent to info@valisluureamet.ee with topic “Nuputamisülesanne”
The crypto challenge seems just as a way to get attention. We are living in times where end-point exploitation is the tool to obtain intelligence. The capability to break ancient substitution cipher is unlikely to help.
Links:
https://geenius.ee/uudis/eesti-luurejuht-kutsub-toole-hakkereid-see-elus-ainulaadne-voimalus/
https://news.err.ee/681856/estonian-intelligence-chief-threat-of-direct-russian-military-attack-low
https://www.valisluureamet.ee/pdf/raport-2018-ENG-web.pdf
https://valisluureamet.ee/pdf/raport-2018-EST-web.pdf
https://news.postimees.ee/4404323/russia-looking-for-agents-of-influence-in-estonia