Some insights:
2015 proved that the continuity of vital services can be affected, or even crippled, by simple ransomware campaigns that weren’t even intended to disrupt those services.
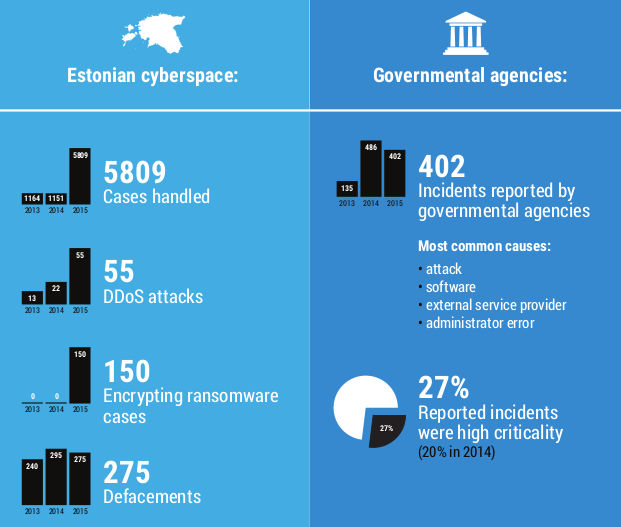
Around-the-clock manned monitoring of Estonian cyberspace has taken place since the summer of 2015. We also adopted new and improved monitoring technologies.As a result of the around-the-clock monitoring, we have prevented, discovered, and reacted to signifcantly more security incidents than in past years.
In 2015, the lessons learned from the CyberHEDGEHOG 2015 exercise, the amendment of the Emergency Act, and the adoption of the European Union Network and Information Security Directive (NIS) confrmed the need for a clear cyber security law that takes into account modern conditions.
In 2015 we became convinced about the necessity of thoroughly analysing both the legal questions associated with using cloud technologies and the risks connected to the integrity and confidentiality of data being processed in the cloud as well as the need to develop sufficient security measures to minimise those risks.
While European Union structural funds have been a welcome source of support for Estonian cyber security development, and indeed for the whole country’s IT development, it is clear that this situation is not sustainable for the country in the long term.
Links:
https://www.ria.ee/public/Kuberturvalisus/2015-RIA-Annual-cyber-report.pdf