This page describes an interdisciplinary research questioning the Estonian digital signature scheme compliance with the national and European Union legal requirements. Our findings put into question the validity of a vast majority of Estonian digital signatures created until today.

Questions & Answers
What is the problem and its impact?
Estonian law has required establishing the time of signing as an intrinsic part of a digital signature.
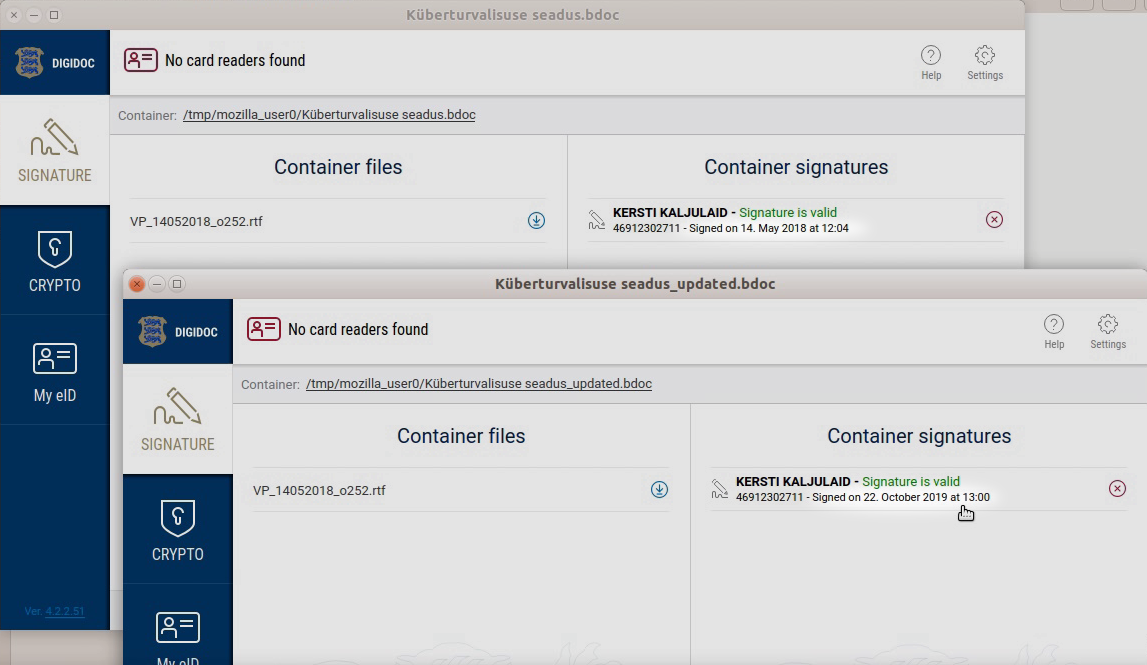
This can be seen in the “Signed on” field of the state-provided digital signature validation software
when looking at a digitally signed document. The main problem is that contrary to the legal requirement,
the Estonian digital signature does not allow us to determine the time when the signature was actually given
(when the PIN code was entered). A common misconception
is that the timestamp of the signature allows us to
establish the precise time when a document was signed.
In reality, the timestamp can only prove that the signed document existed at some particular time.
Actually, the document might have been signed much earlier as the timestamp can be added later by anyone.
We include a link to a video demonstrating the problem
which shows, how easy it is to modify the
“Signed on” time of a digitally signed legal act downloaded from Riigikogu website.
As shown, no input is required from the actual owner of the digital signature.
The unreliability of the “Signed on” time leads to a related legal problem –
it is not possible to verify whether the digital signature was given in the period when the certificate was valid.
In Estonia, the certificates can be temporarily suspended and their validity later restored.
The timestamp is therefore not able to assure that the signature was given after the validity of a suspended certificate was restored.
For example, if you lose your wallet which contains your ID card and PIN codes,
the person who finds the wallet can forge a digital signature even if the certificates of your lost ID card are in a suspended state.
After the wallet is returned and you reactivate the certificates,
the person who created a signature will now be able to obtain a valid timestamp making the signature valid,
while legally such a signature should not be valid.
Since, as a security measure, all ID card certificates are suspended before ID cards are handed out to the cardholders,
the result is that the validity of digital signatures created using the current ID cards cannot be verified.
Should Estonian government declare all digital signatures invalid?
Only a court can declare a digital signature invalid when a dispute arises. In practice, Estonian courts rely on the official DigiDoc software to verify the signatures of digitally signed documents. The courts are not aware that the validation algorithm implemented in DigiDoc is not able to validate signatures according to the legal requirements. The party contesting the validity of a signature would need to convince the court that the signature does not comply to the legal requirements and cannot be verified according to law. Currently we are not aware of any judgements where this issue has been raised.
What should the authorities do?
For the legislator we suggest: 1) abandoning the requirement to establish the time of signing, and 2) establishing that certificates are valid from the beginning of their issuance until expiration or irrevocable revocation. The situation where a suspended certificate can become valid again should be avoided if the current technological solutions are used.
To eliminate security risks, the certificate should be issued after the ID card has been delivered to the cardholder, and the certificate revocation and renewal process should be adjusted to provide the same level of convenience as the current certificate suspension mechanism provides.
For quick implementation, as a minimum, the “Signed on” time shown in the state-provided validation application should be updated (e.g., renamed to “Validated on”) to reflect the technical reality and unreliability of the time shown.
What should people do?
We recommend ending the practice of referring to the time of signing as a date of legal significance in electronic contracts. Instead, all important dates should be specified in the document to be signed. If people want to obtain stronger evidence about the time period in which the signature could have been given, the currently available software can be used to double-sign the digital signature container immediately after signing it. This will create cryptographic evidence that the outer signature was given in the time period between “Signed on” time of the inner and the outer digital signature containers.
Until the authorities resolve the problems, people should carefully inspect PIN envelopes when receiving their ID cards and should refuse accepting ID cards if the security envelope is transparent or there are signs that it has been opened. In cases where the certificates of a lost ID card are suspended, and the card is later found, certificate validity should not be restored unless it is absolutely certain that during the suspension period the ID card was not accessible to third parties.
Is it possible to set “Signed on” time to any date?
No. The time shown in the “Signed on” field comes from the time when the timestamp was obtained. However, a valid timestamp of a signature can be obtained by anyone and as many times needed, as long as the signatory's certificate is still valid. This is not a security flaw but a design requirement.
Can the modification of “Signed on” time be detected?
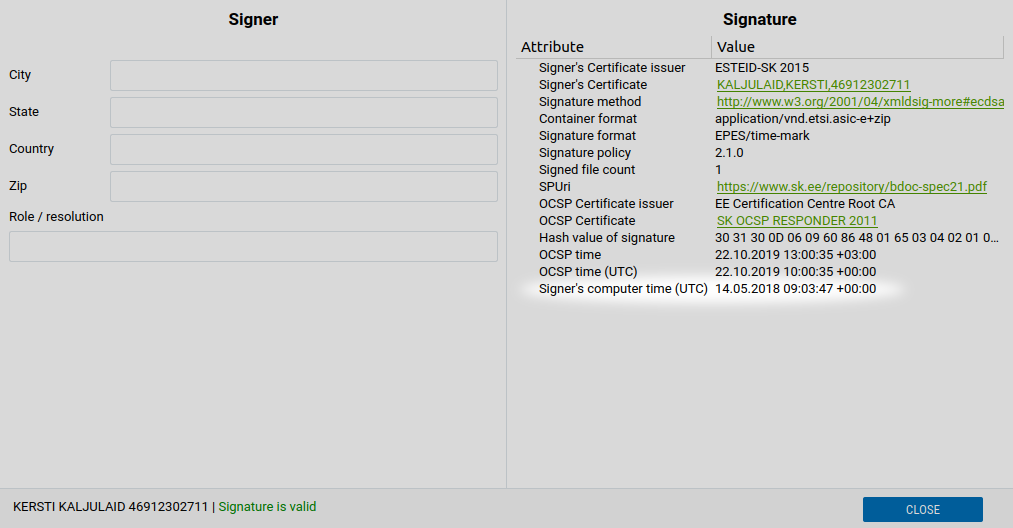
Signed metadata includes the signer's self-reported computer time which can be inspected by clicking on the signature.
If the “Signed on” time is more than a few seconds away from the computer time, it may suggest that the timestamp might have been updated.
However, even if the computer time matches the “Signed on” time,
it cannot be trusted to establish the time of signing,
since at the time of signing this time could have been set to an arbitrary value.
In the example of a suspended certificate, the attacker could plan ahead and change the self-reported computer time
to a future date when he plans to obtain the timestamp.
How does digital signing technically work?
Signing with an ID card itself is an offline operation. There is no trace left of a signature being made.
While legally binding, such a signature can be verified only as long as the signatory's certificate is valid.
To verify the validity of a signature after the signatory's certificate expires or is revoked,
the digital signature container is expected to contain validation data.
To obtain the validation data, the signatory or some other party has to interact with the online services
provided by trust service provider.
Validation data consists of: 1) a cryptographic timestamp proving that signature existed
at some particular moment in time, and 2) a certificate validity response (OCSP response)
proving that after the time specified in the timestamp, the signatory's certificate was still valid.
The timestamp and OCSP response attached to the signature container is not protected by the signatory's signature and therefore
can be modified.
Can’t we just fix the digital signature?
Fixing the technological solution is far from trivial. Even if the Estonian digital signature solution would be redesigned to allow establishing the actual time of signing, it would not be internationally recognized as Estonia has to accept eIDAS qualified electronic signatures which do not allow establishing the time of signing.
Is this an Estonian-specific problem or the problem of EU eIDAS regulation?
The requirement to establish time of signing has been an Estonian-specific requirement – eIDAS does not require that. At the time the Estonian legal framework for digital signatures was drafted, the assumption was made that the timestamp mechanism allows to establish the precise time when the document was digitally signed. We find this assumption to be incorrect.
eIDAS regulation allows member states to implement temporary certificate validity suspension mechanisms but does not demand that member states do that. Any EU member state whose digital signature scheme allows certificate suspension will also produce digital signatures that cannot be verified according to eIDAS requirements. This is because eIDAS digital signature standards do not provide means to establish certificate validity at the time of signing in cases when the certificate after its issuance has temporarily lost its validity. The digital signature schemes used in other countries (e.g., Latvia, Lithuania, Poland, Romania, Ireland, Luxemburg, Malta, and possibly others) are also affected by this problem. We found that only Slovakian law explicitly forbids certificate suspension.
Are signatures created by ID card, Mobile-ID and Smart-ID equally affected?
No matter which type of eID tool is used, the “Signed on” time reported by the digital signature software does not allow establishing the time when the signature was actually given. In case of Mobile‑ID and Smart-ID the service provider may have records about the time when the signature request was sent to the mobile phone. The digital signature itself does not contain that information. This means that neither of these signatures can be used to determine the time of signing.
Contrary to ID card certificates, Mobile-ID certificates are not in a suspended state after their issuance. However, since Mobile-ID certificates can be suspended in their lifetime, Mobile-ID signatures cannot be verified unless there is evidence available proving that the corresponding Mobile‑ID certificate has never been suspended. Smart-ID does not support certificate suspension, therefore, as far as this issue is concerned, the validity of Smart-ID digital signature can be verified.
Why was the problem found only now?
To some extent the problem has been known or suspected by the people behind the digital signature scheme already for years. However, until now no-one has demonstrated or analyzed the practical and legal consequences of it. Such interdisciplinary research is not often done outside the institutions responsible for the Estonian digital signature scheme.
Have Estonian authorities been informed?
We have disclosed our findings and discussed the problems with Estonian Information System Authority (Riigi Infosüsteemi Amet – RIA) and Ministry of Economic Affairs and Communications (Majandus- ja Kommunikatsiooniministeerium) in summer 2019. However, currently we are not aware of any action plan to solve the issues. We will keep this page updated as we learn about the progress made in solving the issues.
How does all of this affect i-voting?
We have not analyzed i-voting in our research. Technically the risk seems to be limited. Even if the attacker could sign an i-vote in the period when the certificate was suspended, the attacker would still need a valid (non-suspended) eID tool of the victim to submit the forged i-vote to the i-voting servers. Legally, according to law, voters confirm their electronic votes by a digital signature. If the validity of the digital signature can be challenged, the vote could also be challenged.
Who is behind this research?
This interdisciplinary research was conducted by Tõnu Mets (Advokaadibüroo Mets, attorney at law, visiting lecturer at UT School of Law) and Arnis Paršovs (researcher at UT Institute of Computer Science) during their doctoral studies. The article “Time of signing in the Estonian digital signature scheme” analyzing the problems has been published in the journal “Digital Evidence and Electronic Signature Law Review”.
Timeline & Updates
- 2016-07-02: The idea to conduct interdisciplinary research on this problem was born.
- 2019-07-05: Meeting with RIA to discuss the problems.
- 2019-11-01: Journal article published.
- 2019-11-04: This website was published and the problem disclosed to media.
- 2020-07-07: Laura Kask (UT/Proud Engineers) and Kristiina Laanest (RIA) published an article suggesting to establish the time from timestamp as the time of signing. The article, however, fails to address the issues raised in this research.
- 2021-05-27: ETSI released the standard ETSI TS 119 172-4 V1.1.1 on the validation of eIDAS qualified electronic signatures. The standard explicitly states that the validation mechanism is only able to support certificate suspension, where a certificate is considered as having been valid during the suspension period in case the certificate suspension is later terminated. In another words, the technology currently standardized by ETSI and IETF standards is not able to handle the certificate suspension mechanism that is used in Estonia.
- 2021-09-01: A thesis research topic Trustworthy signing time for the Estonian digital signature has been published describing the options to tackle this problem.
Media
- UT: University of Tartu scientists found a weakness in digital signing and offered their solutions
- ERR: Tartu researchers found a problem in digital signing and offered a solution (in Estonian)
- RIA: University of Tartu research: Europe needs to specify how digital signatures are given
- Postimees: Video: Researchers proved that the time to issue an Estonian digital signature can be falsified (in Estonian)
- Postimees: Researchers at the University of Tartu found a weak point in digital signing (in Estonian)
- Delfi: UT researchers found a weak point in digital signing (in Estonian)
- Delfi: VIDEO | Weakness of the ID-card: it is so easy to change the digital signature of Kersti Kaljulaid (in Estonian)
- Geenius: Video: researchers faked President Kaljulaid's digital signature date (in Estonian)
- Geenius: RIA: To date, there are no known cases of digital signature timestamp abuse (in Estonian)
- Geenius: RIA: Faking of digital signature date is not comparable to ID card crisis (in Estonian)